One of my friends is very bullish on cryptocurrency. He claims that it is the future of money and has the potential to change the world we live in. I couldn’t agree more. However, just like most of the speculators, he finds it annoying when someone talks about the underlying blockchain technology. He might be great at reading the charts, but lack of understanding of how Bitcoin works is something that is just outright crime. So when I asked him what is hash function, he laughed it off. Are you the friend I am referring to? If yes, then read on. If you are reading this, you obviously are into cryptoverse. Which by the way, also means that you must have come across the term: Proof of Work.

But before I jump into proof of work, I want to touch upon a rather spectacular concept of a hash function. It forms the basis of proof of work and very soon you’ll know how. As always, the topics that are explained after I try and test on my mother. Only when she says that she has an idea of what I am speaking, I resort to writing. So, trust me on this. This one would have no fancy words whatsoever. Let’s get started!
What is Hash Function?:
To put it into simplest terms, hash is nothing but a random string of numbers that represents some kind of input data. Think of it as a converter. You put something from one end and you get a string of numbers from the other side. You can put anything here. A text, an image, even a single character for that matter.

So, if you put P.A.N.D.A.T.E.C.H.I.E. as an input to a hash function, you would get something like 123724123123 on the other side. As simple as that.
With that being said, hash function has a unique set of properties. These properties make it much more useful. Let’s explore each of these traits in detail.
A. Fast:
A hash function is lightning fast. Anything that you input from one end, will yield the output string instantaneously. This is critical as hash has to be a randomly generated number. And if someone is guessing a specific hash, they need to do that as soon as possible (more on this shortly)

B. Deterministic:
This means that every time you put a specific input, the hash function should yield the same output. For example, if you put PANDA as an input and the output is 12345, every time you put in PANDA, the output should be the same.
C. Collision Resistant:
No we are not talking about real collisions. But this one is not fundamentally very different from that. While some of you might have guessed where this is headed, for others, collision resistance is the property of hash functions that allows no two inputs to have a same output. Makes sense right?

When I say two inputs, the difference between them can be miniscule. For example, even PANDA and PaNDa should yield a different output.
D. One Way:
Yup. You guessed it right. Hash functions are one way only. That means you can create a random string of numbers from a hash function using any input, however, you cannot trace back an input using those numbers. In a similar example, there should be no way for you to learn that 12345 stands for PANDA.
While reverse engineering is a legit strategy in most of the products, it shouldn’t be possible for a hash function.
E. Avalanche Effect:
Once again, this property has a lot to do with how entire scheme of hash functions fits into Bitcoin’s infamous proof of work. Avalanche effect refers to the attribute that would change the output of a hash function dramatically even if the input is changed slightly.

For example, if the input “TECHIE” is changed to “TECHY”, the two outputs generated would be so different that they would have no correlation with each other whatsoever. It would be almost impossible to draw a connection between these two outputs.
How is Hash Function used in Mining?
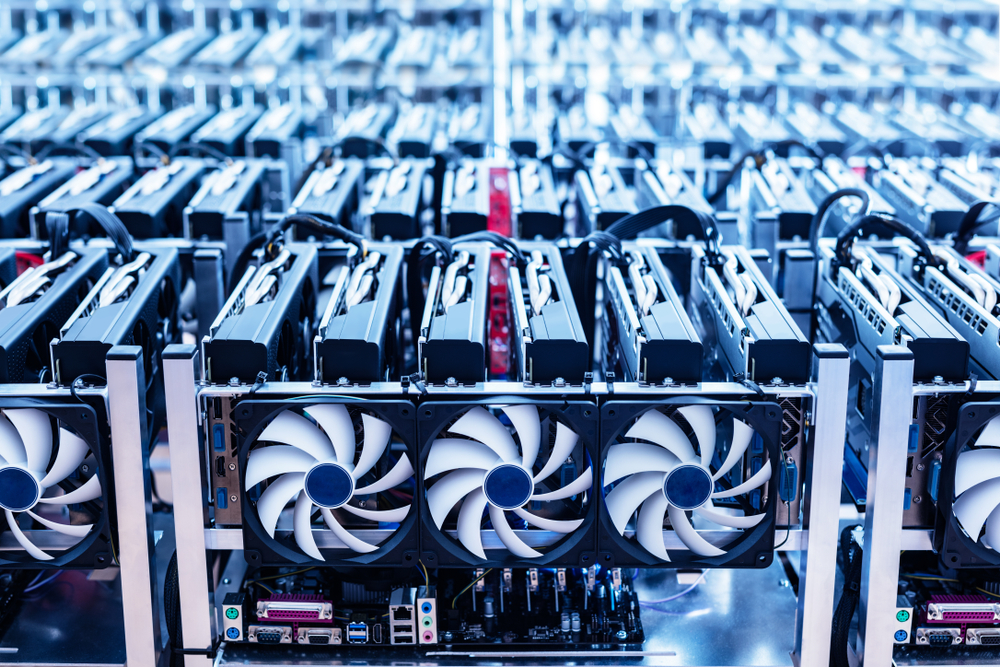
Now that you are aware of properties of a hash function, let’s find out how it used in mining. What is proof of work? Very often we hear that miners solve a complicated mathematical puzzle to prove the work has been done. But what is this complex problem?
Well, it’s nothing but a hash function called SHA-256. Miners use the following inputs in a hash function:
- Transaction Data of the block
- Reference number (also called hash number) of the previous block
- Work number (also called nonce)

They club these inputs in such a way that output generated (from hash function) is in such a way that it starts with four ZEROES. Miner to reach this hash output the fastest wins the right to mine the next block.

How do they reach this number? It’s purely guess work. Miners already have the reference number of previous block and transaction data. What they do is start guessing the work number (nonce) from 0,1,2 till 100 to 1000 until they by accident reach a number which would generate the desired hash output.
This also means that more the computational power, better are your chances of guessing this work number faster and hence winning this race.
Conclusion:
Anyone who believes in technology would know that this is no less than magic. I still wonder the thought process that would’ve gone behind using these methodologies to come up with world’s first permissionless, trust less, decentralized peer to peer transaction system.
If you are as awestruck as me, hit me up. I can talk about it endlessly!
Got questions? Want to take it to the next level? Reach out to me using your preferred platform from the links below
Until next time..
Psst.. Struggling to save money?
I just managed to save Rs. 10,000 by investing my ‘Chillar (Change)’ in mutual funds. Investing amounts like Rs. 5, 8, 25, 45.. and 4 months later, Boom! I have 10 grand to spare. Interested in knowing how I did it? Read more here.
For our beloved “non readers”, I also do quick carousels on these topics over Instagram. Come join the fun. Hit me up here.
On a side note, I use CoinMarketCap for all my crypto related research. You can access it through multiple modes. Sharing the links below:

3 responses to “What is Hash Function in Blockchain? How is it used in Proof of Work?”
[…] ask her if the consensus mechanism is based on ‘Proof of Work‘ or ‘Proof of Stake’ or something […]
[…] Without going into too much of technicality, this is achieved through making people solve a complicated mathematical puzzle. If you are interested in understanding how this puzzle works I would recommend that you read this post. […]
[…] all started with Bitcoin and its power intensive consensus mechanism: proof of work (PoW). Think of it like this; In a centralized system, all computation is done centrally by a […]